By Thorsten Meyer | ThorstenMeyerAI.com | February 2026
Executive Summary
Every major computing paradigm has created a governance layer worth billions. AI agents are next.
In January 2026, an open-source AI agent framework called OpenClaw crossed 164,000 GitHub stars, making it one of the fastest-growing open-source projects in history. That same month, security firm Koi Security audited 2,857 “skills” — plugin-like capability packages — in OpenClaw’s public ClawHub registry. They found 341 that were explicitly malicious. Credential stealers, backdoors, reverse shells, crypto-mining payloads, all disguised as helpful automations.
The timing was almost poetic. At the very moment OpenClaw hit critical mass, the security incident exposed how dangerous that success could be without governance.
But here’s what happened next: the demand didn’t go away. If anything, it sharpened. Every VP of Engineering who blocked OpenClaw still has the same problem: alert-fatigued SRE teams drowning in noise (73% of organizations have experienced outages linked to ignored alerts), 70% of SREs reporting on-call stress impacts burnout and attrition, and runbooks that exist but nobody executes.
The AI agent market is projected to grow from $7.84 billion in 2025 to $52.62 billion by 2030 — a CAGR of 46.3%. Eighty-five percent of enterprises are expected to implement AI agents by end of 2025, and 96% plan to expand in 2026. But confidence in fully autonomous AI agents has fallen from 43% in 2024 to 22% in 2025.
The demand is exploding. The trust is collapsing. The gap between those two curves is the market opportunity.
The question is no longer whether enterprises will deploy AI agents at scale. It’s who will make it safe enough to do so.
The Playbook Is Already Written
The history of enterprise software follows a predictable arc. A powerful open-source technology achieves developer adoption. Enterprises want it but can’t use it without governance, security, and compliance. A company builds the enterprise layer and captures enormous value.
The pattern is so consistent it’s almost boring. But it keeps working because the underlying dynamic never changes: developers adopt the best tools, and enterprises need guardrails around them.
| Open-Source Project | Enterprise Layer | Current Market Cap | What They Added |
|---|---|---|---|
| Apache Kafka | Confluent | $10.8B (acquired by IBM) | Schema registry, monitoring, managed service |
| Git | GitLab | $6.0B | CI/CD, governance, compliance |
| Elasticsearch | Elastic | $7.0B | Security, observability, enterprise search |
| Terraform | HashiCorp | $7.1B (acquired by IBM) | Policy-as-code, collaboration, governance |
| MongoDB | MongoDB | $30.3B | Enterprise security, backup, managed Atlas |
That’s over $60 billion in combined market capitalization created by building governance and enterprise features on top of open-source projects.
The pattern has three phases:
Phase 1 — Developer Love. The open-source project gains traction because it solves a real problem elegantly. Developers adopt it, build on it, and create a community.
Phase 2 — Enterprise Friction. Companies want to use the tool but can’t get past security, compliance, and governance requirements. CISOs block it. Procurement stalls. Shadow adoption grows.
Phase 3 — Enterprise Layer. A company builds the governance, security, and management features that bridge the gap. It captures value because the switching costs — integrations, policies, audit trails — compound over time.
OpenClaw is deep into Phase 2. The question is who builds Phase 3.
Why OpenClaw Matters
Not Another Chatbot Framework
OpenClaw isn’t a chatbot. It’s an AI agent framework that lets users control their computers via natural language through the messaging apps they already use — WhatsApp, Slack, Telegram. Originally published in November 2025 by Austrian developer Peter Steinberger under the name “Clawdbot,” it was renamed to “Moltbot” on January 27, 2026 after trademark concerns from Anthropic, then to “OpenClaw” three days later.
Its community has built 3,000+ skills covering everything from incident response to email triage to infrastructure automation. For DevOps and SRE teams, the promise is transformative:
| OpenClaw Capability | Impact |
|---|---|
| Automated incident response | 85% auto-resolution of routine incidents |
| Runbook execution | Runbooks that actually run, not just sit in Confluence |
| Alert triage and routing | ML-powered noise reduction of 80–90% |
| 24/7 coverage | No more 3am pages for known issues |
| Cross-platform integration | WhatsApp, Slack, Telegram — meets teams where they are |
The numbers behind the problem OpenClaw solves are staggering. The 2025 Catchpoint SRE Report found that overloaded teams see MTTR stretch to 4 hours per incident. Uptime Institute reports a significant share of outages cost over $100,000 each. Developer toil consumes an estimated $9.4 million per year at enterprise scale. And 78% of developers spend 30% or more of their time on manual tasks that could be automated.
OpenClaw isn’t a nice-to-have. It’s a direct answer to a problem that costs enterprises millions annually.
The Security Incident That Changed Everything
But talk to the people who actually have to approve these tools — the CISOs, the VPs of Engineering, the compliance leads — and you hear a different story.
On January 27, 2026, the same day OpenClaw rebranded from Clawdbot, Koi Security published an audit of ClawHub, the project’s public skill registry. Of 2,857 skills analyzed, 341 were explicitly malicious:
- Fake cryptocurrency trading tools installing Atomic Stealer malware
- Typosquatted packages that exfiltrate credentials
- Backdoored utilities establishing reverse shells
- Ranking manipulation to manufacture popularity for malicious skills
Days later, researchers disclosed CVE-2026-25253 — a one-click remote code execution vulnerability that works even on instances configured to listen only on localhost, because the victim’s browser initiates the outbound connection.
The Register called OpenClaw a security “dumpster fire.” Cisco’s security team published a blog titled “Personal AI Agents like OpenClaw Are a Security Nightmare.” Tenable released guidance on mitigating OpenClaw’s agentic AI vulnerabilities.
The security community’s verdict was unanimous: OpenClaw is powerful, popular, and dangerously ungoverned.
And yet — the GitHub stars kept climbing. From 100,000 to 164,000 in a matter of weeks. The demand didn’t flinch.
The Five Blockers
When enterprise engineering and security leaders evaluate OpenClaw, the same five objections surface in nearly every conversation:
1. No Audit Trails
Every action an AI agent takes — every shell command, every file access, every API call — needs to be logged with full context. User, timestamp, input, output, result. Without this, you can’t debug incidents, you can’t prove compliance, and you can’t hold anyone accountable.
SOC2 requires demonstrable evidence that access to systems is logged and reviewable. HIPAA requires audit controls. GDPR requires records of processing activities. OpenClaw, in its current form, provides none of this.
2. No Access Controls
OpenClaw makes no distinction between a junior engineer and a senior SRE. There’s no role-based access, no principle of least privilege. The same person who should only be reading logs can restart production databases.
In any enterprise environment, this is a non-starter. The principle of least privilege isn’t a suggestion — it’s a compliance requirement.
3. No Security Scanning
The public ClawHub registry is the npm of AI agent skills — powerful, vast, and dangerously trusting. The 341 malicious skills discovered in January were just the ones that got caught. Agentic supply chains include tools, plugins, prompt templates, model files, and external MCP servers — many fetched dynamically at runtime. Any compromised component can alter agent behavior or expose data.
4. No Secrets Management
API keys and credentials are scattered across skill files, environment variables, and Slack threads. There’s no centralized vault, no access scoping, no rotation. In an environment where an AI agent can execute arbitrary commands, unsecured credentials are a breach waiting to happen.
5. No Team Features
OpenClaw was built for power users, not organizations. There’s no concept of teams, no approval workflows for sensitive actions, no multi-agent coordination. For a single developer automating their own workflow, this is fine. For a 200-person engineering organization, it’s unmanageable.
Each of these is a hard blocker for enterprise adoption. Together, they form a wall.
The Governance Layer: What It Looks Like
Don’t Rebuild — Wrap
The solution isn’t to rebuild OpenClaw from scratch. That would throw away the 164,000-star community, the 3,000+ skills, and the momentum that makes the platform valuable. The open-source-to-enterprise pattern has never worked by replacing the project — it works by wrapping it.
Confluent didn’t rebuild Kafka. GitLab didn’t rebuild Git. Elastic didn’t rebuild Lucene. They built governance, security, and management layers that made the underlying technology enterprise-safe without sacrificing what developers loved about it.
The governance layer for OpenClaw needs to do six things:
| Capability | What It Does | Why It Matters |
|---|---|---|
| Full audit logging | Every agent action recorded — user, timestamp, input, output, result | SOC2, HIPAA, GDPR compliance; incident debugging |
| Role-based access control | Define who can run what agents with what permissions, synced with SSO | Principle of least privilege; compliance requirement |
| Private skill registry | Curated, malware-scanned repository replacing ClawHub free-for-all | Eliminates supply-chain attack vector |
| SSO integration | Okta, Azure AD, Google Workspace | Enterprise identity from day one |
| Blast radius controls | Policy-defined boundaries for what agents can access and modify | Limits damage from misconfigured or compromised agents |
| Approval workflows | Human-in-the-loop for sensitive actions with Slack notifications | Risk management without killing velocity |
The key design principle: zero friction for the happy path. Agents work exactly as before. They’re just governed now.
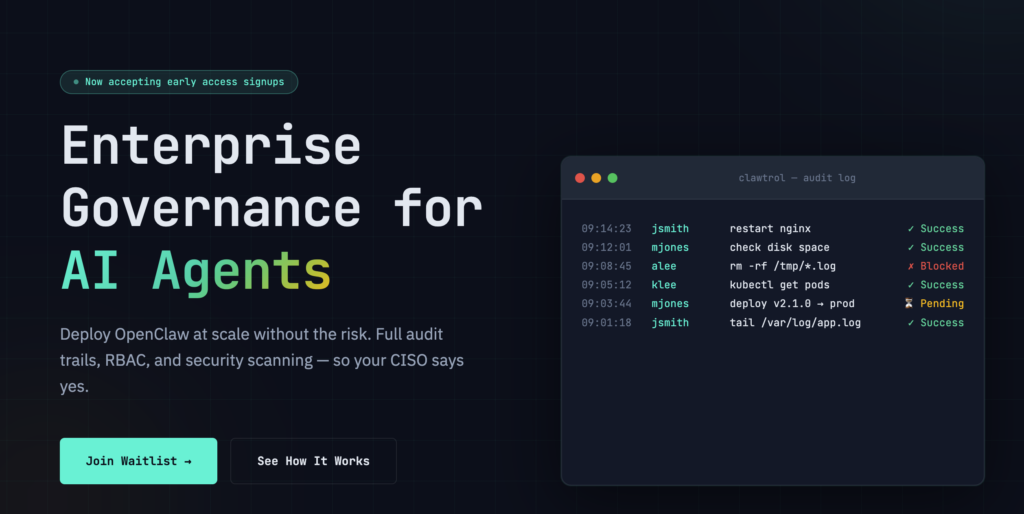
This is precisely what Clawtrol (clawtrol.com) is building. Clawtrol sits between the enterprise and OpenClaw’s core. When an agent receives a command, Clawtrol’s SDK intercepts it, checks permissions, validates against blast radius policies, and logs the full action — all in under 50 milliseconds. If allowed, the agent executes normally. If blocked, the denial is logged and the user gets a clear explanation. If escalation is required, the approval workflow kicks in.
Setup takes 30 minutes. Install the SDK, connect to Clawtrol, assign policies. Done.
The Market Math
The Demand Curve
The global AI agent market projections tell a consistent story, even as specific numbers vary across research firms:
| Research Firm | 2025 Market Size | 2030 Projection | CAGR |
|---|---|---|---|
| Grand View Research | $7.84B | $52.62B | 46.3% |
| BCC Research | $8.0B | $48.3B | 43.3% |
| MarkNtel Advisors | $5.32B | $42.7B | 41.5% |
| Precedence Research | $7.92B | — ($236B by 2034) | — |
Enterprise AI agents represent roughly 30% of the total market — putting the serviceable addressable market at approximately $15.8 billion by 2030.
But the more telling number is the adoption pressure:
- 85% of enterprises expected to implement AI agents by end of 2025
- 96% plan to expand AI agent usage in 2026
- 79% already report some level of agentic AI adoption
- AI spend increasing 40% year-over-year
- Confidence in fully autonomous agents: down from 43% to 22%
That last number is the one that matters most. Adoption is accelerating. Trust is declining. Every enterprise deploying AI agents needs governance, and the governance doesn’t exist yet.
The Cost of Not Governing
The business case for AI agent governance isn’t abstract. It’s a line item:
| Cost Category | Annual Impact | Source |
|---|---|---|
| L1 incident response waste | $200K+ per mid-size org | Engineering leader surveys |
| Alert fatigue waste | $150K+ in engineer time | Catchpoint SRE Report 2025 |
| Developer toil (manual tasks) | $9.4M at enterprise scale | Industry analysis |
| Average outage cost | $100K+ per incident | Uptime Institute |
| Failed SOC2 audit | 6-month enterprise deal delay | Compliance industry data |
When OpenClaw can auto-resolve 85% of routine incidents but can’t get past the CISO’s desk, the cost isn’t the governance subscription fee — it’s the $350K+ in operational waste that persists every year the organization waits.
Why Now — And Why Not Later
The Timing Window
Timing windows in enterprise software are measured in months, not years. Three conditions are converging simultaneously:
Critical mass achieved. OpenClaw crossed 100,000 stars in January and reached 164,000 by early February. The community is self-sustaining. The skill ecosystem is rich. Developer adoption is no longer a question.
Security urgency created. The 341 malicious skills and CVE-2026-25253 made OpenClaw governance a boardroom conversation overnight. Every CISO in the Fortune 500 now has OpenClaw on their risk register.
Enterprise budgets unfreezing. AI spending is increasing 40% year-over-year. The 2025 wait-and-see period is over. Enterprises are deploying — they just need the governance layer to do it safely.
The companies that built enterprise layers on open-source projects all share one trait: they moved fast during the window and locked in design partners before the market got crowded. Confluent did it with Kafka. Elastic did it with Elasticsearch. HashiCorp did it with Terraform. The playbook is clear.
The risk of waiting isn’t that the opportunity disappears — it’s that someone else takes it.
The Competitive Landscape
Right now, the competitive landscape for OpenClaw enterprise governance is remarkably open. No funded competitor has established category leadership. The incumbents — ServiceNow, Datadog, CrowdStrike, PagerDuty — have AI agent capabilities on their roadmaps but haven’t shipped purpose-built OpenClaw governance.
This won’t last. The window is 6–12 months before well-funded incumbents or new entrants arrive. First-mover advantage in enterprise software isn’t about technology — it’s about the relationships, integrations, and switching costs that compound over time.
The Competitive Moat

Clawtrol’s competitive moat has five layers, each reinforcing the others:
1. Community leverage. 164,000+ GitHub stars and 3,000+ skills represent years of community building that no new entrant can replicate. Building on OpenClaw’s community is a structural advantage.
2. Trust and security brand. “The secure way to use OpenClaw” is a positioning that, once established, becomes self-reinforcing. In enterprise software, the vendor associated with governance owns the purchase decision.
3. Enterprise feature depth. RBAC, audit, compliance, SSO — these are table stakes for enterprise, but each one is months of engineering work. Head start matters because the features compound.
4. Switching costs. Once an organization’s skills, policies, roles, and integrations live in Clawtrol, moving away is painful and expensive. This grows with every quarter in production.
5. Data advantage. Aggregate learnings across customers — which policies work, which skills are risky, what patterns indicate compromise — create intelligence that improves the product for everyone. This is a network effect that competitors can’t buy.
The Business Model

Clawtrol follows the proven SaaS subscription model with per-seat pricing, benchmarked against the DevOps tools it complements or replaces:
| Comparable Tool | Per-User/Host Pricing | What Clawtrol Replaces |
|---|---|---|
| PagerDuty | $21–49/user/month | Alert routing + L1 response |
| Datadog | $15–34/host/month | Monitoring-to-action gap |
| Snyk | $52–98/dev/month | Supply-chain security scanning |
| Clawtrol | Competitive | Governance + audit + access control |
Target unit economics:
| Metric | Target |
|---|---|
| Average contract value | $8,000 |
| Customer acquisition cost | $4,000 |
| Lifetime value | $24,000 |
| LTV:CAC ratio | 6:1 |
| Gross margins | 85% |
| Payback period | 6 months |
| Net revenue retention | 120% |
The expansion motion is natural. Land with the DevOps/SRE team that has the most acute pain. Expand to security teams demanding compliance visibility. Then to platform engineering organization-wide. Each new team deepens the integration and raises the switching cost.
The Long-Term Vision
Clawtrol starts as enterprise governance for OpenClaw. But the endgame is larger — and the roadmap follows the same trajectory as every successful open-source enterprise company.
| Timeline | Capability | Market Position |
|---|---|---|
| Year 1 | Governance for OpenClaw — audit, RBAC, security scanning | Category leader for OpenClaw enterprise |
| Year 2 | Multi-agent orchestration, self-hosted deployment for regulated industries | Platform for agentic workflows |
| Year 3 | Support for any agent framework, full lifecycle management, AI anomaly detection | Universal AI agent control plane |
The long-term vision: Clawtrol becomes to AI agents what Kubernetes became to containers — the universal control plane. Every enterprise running AI agents will need observability, policy enforcement, and lifecycle management. The platform that establishes itself as the standard for OpenClaw governance is perfectly positioned to expand into that broader role.
Strategic acquirers in this space include ServiceNow, Datadog, CrowdStrike, and Microsoft — all of which need AI agent governance capabilities and would prefer to buy category leadership rather than build it.
The Bottom Line
We’re standing at the intersection of three curves: AI agent adoption going exponential, enterprise compliance pressure intensifying, and a community-driven platform that’s captured developer mindshare but can’t yet cross the enterprise threshold.
This isn’t a speculative bet on future technology. OpenClaw exists today — 164,000 stars and climbing. The demand exists today — 96% of enterprises plan to expand AI agent usage in 2026. The 341 malicious skills exist today. The CVE-2026-25253 vulnerability exists today. The gap between what enterprises want and what they can safely deploy is real, measurable, and growing.
The open-source-to-enterprise playbook has created over $60 billion in market capitalization across Confluent, GitLab, Elastic, HashiCorp, and MongoDB. The pattern is so reliable that the only real question is timing.
OpenClaw is the next instance of this pattern. The governance gap is the market. And the window is open — but not for long.
The infrastructure for the next computing paradigm isn’t the AI model. It’s the governance layer that makes the model safe to deploy. And right now, that layer is being built.
Thorsten Meyer writes about AI strategy for enterprise leaders who’d rather read the security audit than the press release. Follow his work at ThorstenMeyerAI.com
Disclosure: This article includes analysis of Clawtrol (clawtrol.com), an enterprise governance platform for OpenClaw. Thorsten Meyer’s analysis reflects publicly available information and independent assessment of the AI agent governance market.
Sources:
- Thorsten Meyer AI: The AI Agent Governance Gap — And Why It’s a Billion-Dollar Problem
- CNBC: From Clawdbot to Moltbot to OpenClaw — Meet the AI Agent Generating Buzz and Fear
- The Register: DIY AI Bot Farm OpenClaw Is a Security “Dumpster Fire”
- Cisco: Personal AI Agents like OpenClaw Are a Security Nightmare
- Tenable: Clawdbot — How to Mitigate Agentic AI Security Vulnerabilities
- Authmind: OpenClaw’s Malicious Skills — Agentic AI Supply Chain Security
- Open Source For You: AI Assistant OpenClaw Hosts Hundreds of Crypto-Stealing Malicious Plugins
- TechRadar: OpenClaw Malicious Skills Still Trying to Trick Victims
- Adversa.ai: OpenClaw Security 101 — Vulnerabilities & Hardening 2026
- AIKIDO: OWASP Top 10 for Agentic Applications 2026
- Catchpoint / Runframe: State of Incident Management 2025 — The AI Paradox
- IBM: Alert Fatigue Reduction with AI Agents
- incident.io: Alert Fatigue Solutions for DevOps Teams
- GlobeNewsWire: AI Agents Market to Grow 43.3% Annually Through 2030
- Yahoo Finance: AI Agent Market Forecast to Reach $42.7 Billion by 2030
- Warmly: 35+ AI Agent Statistics — Adoption & Insights 2026
- DemandSage: AI Agents Market Size, Share & Trends 2026–2034
- Scientific American: OpenClaw Is an Open-Source AI Agent That Runs Your Computer